SCF C|P-RMM
This section details the Secure Controls Framework — Cybersecurity & Data Privacy Risk Management Model (SCF C|P-RMM). [1] [2] The perspective provided by such framework is central to the book, as it clearly defines Threats versus Vulnerabilities and Risks.
Summary
The SCF C|P-RMM is part of a comprehensive Risk Management Ecosystem. This “meta-framework” unifies a diversity of controls from standards like NIST, ISO, and GDPR into a single cohesive practice. Its core principle is clear: Cybersecurity teams manage Controls, but business units own Risk. Rather than battling inevitable external threats, the framework focuses on aligning internal controls with the organization’s risk tolerance.
Figure 1 illustrates this Risk Management Ecosystem. It depicts Risk not as an isolated event, but as the calculated result of a Threat exploiting a Vulnerability. This visual distinction is critical: Threats are inevitable, but Vulnerabilities are manageable. By strengthening controls, organizations break the chain before Risk is realized.
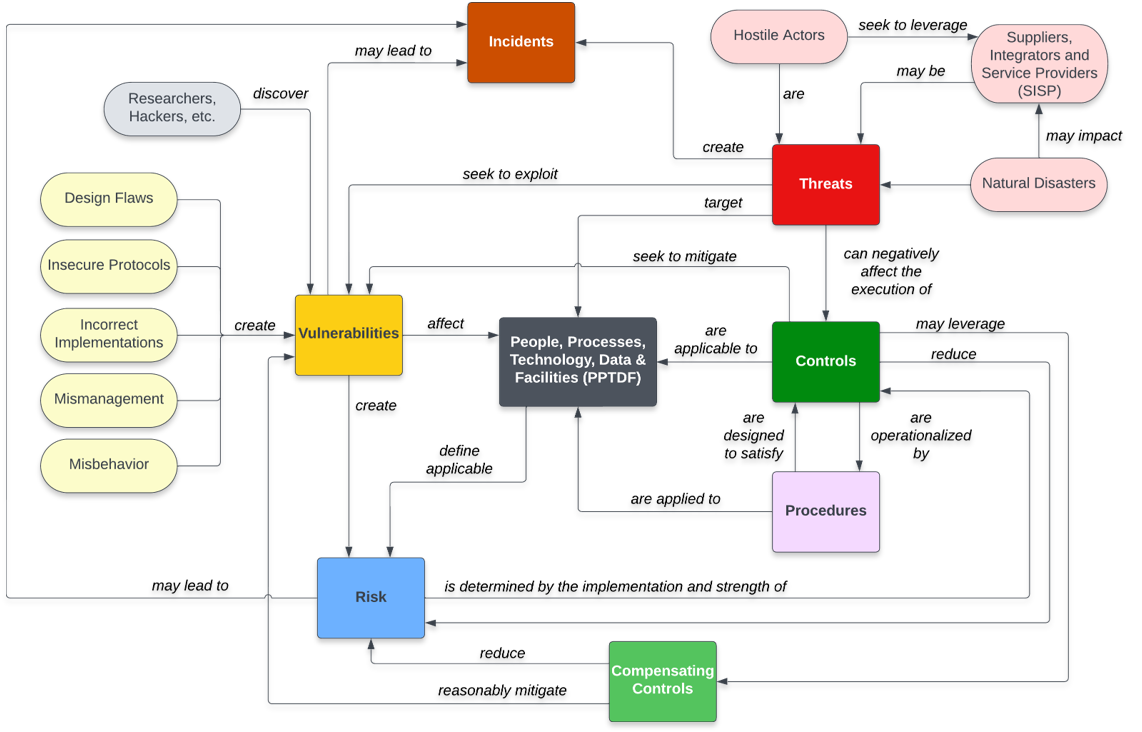
Figure 1: Risks vs Threats vs Vulnerabilities according to SCF C|P-RMM.
Threat
A Threat is defined by the SCF C|P-RMM as a person or thing likely to cause damage or danger. It represents the potential negative action or event whether natural (e.g., floods, earthquakes) or man-made (e.g., hackers, insiders) that could impact the organization. Threats are generally external to the control environment or inevitable forces that the organization must prepare for but cannot directly eliminate.
Vulnerability
A Vulnerability is associated with Control Deficiencies. It is a weakness or gap in the organization’s defenses where a Control is either missing, ineffective, or failing to function as expected. When a Threat materializes, it is the presence of a Vulnerability that allows the Threat to cause actual harm.
Risk
Risk is the situation where someone or something valued is exposed to danger, harm, or loss. It is the result of a Threat exploiting a Vulnerability. In the SCF C|P-RMM model, risk is the business’s quantifiable or qualitative potential for loss.
Critique
The “Threat Catalog,” as found in SCF C|P-RMM, is often seen as broad beyond the point of being useful. Listing “NT-13 Volcanoes” alongside “MT-2 Hacking” flattens the threat landscape. For 99% of businesses, volcanoes are irrelevant to Cybersecurity, yet they occupy space in the framework, demanding mental energy to scope out. The noise obscures the signal of actual, probable threats.
Adaption for GenAI Security Purposes
In the spirit of the above critique, Gurple takes the approach of building on top of the SCF C|P-RMM framework, by going one level deeper into the “Threat Catalog.” The Threats discussed in Gurple, will be, then, more specific and relevant to GenAI Security. This specialized approach is detailed in the Threats chapter.